

When your existing endpoint security doesn’t provide the advanced attack visibility and response required – adding easy- to-use Bitdefender Endpoint Detection and Response (EDR) quickly and effectively strengthens your security operations.


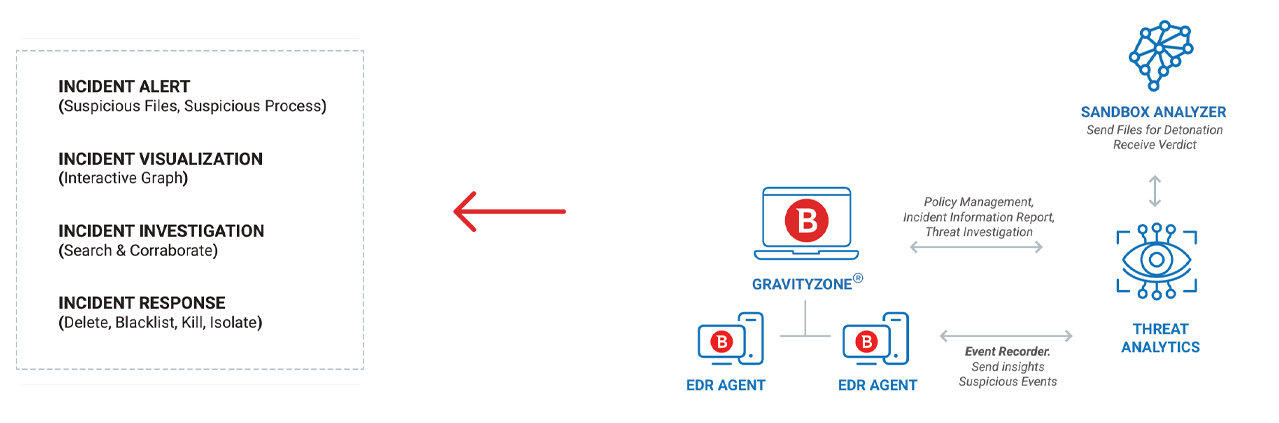
Bitdefender EDR is a cloud-delivered solution built on the Bitdefender GravityZone cloud platform. EDR agents are deployed on your organization’s endpoints. Each EDR agent has an event recorder that continuously monitors the endpoint and securely sends insights and suspicious events to the GravityZone cloud. In Gravity Zone, the Threat Analytics module collects and distils endpoint events into a prioritized list of incidents for additional investigation and response. It sends suspicious files for detonation in the Sandbox Analyzer then uses the sandbox verdict in EDR’s incident reports. The EDR real-time dashboard can be accessed from any device to enable administrators to see alerts and visualizations, then investigate and respond effectively to threats.
Continuously analyses your organizational risk using hundreds of factors to identify, prioritize and provide guidance on mitigating user, network and endpoint risks.
Detects advanced threats including file-less attacks, ransomware and other zero-day threats in real-time. Complements your existing endpoint security solution to strengthen detection.
Cloud-based event collector continuously distils endpoint events into a prioritized list of incidents for additional investigation and response.
Continuous endpoint event monitoring that feeds events to threat analytics to build threat visualizations of the events involved in an attack.
Automatically executes suspicious payloads in contained virtual environment. The threat analytics module then uses this analysis to make decisions on suspicious files.
Query the events database to uncover threats. Uncover MITRE ATT&CK techniques and indicators of compromise. Up to the minute insight into named threats and other malware that may be involved.
Easy-to-understand visual guides, enriched with context and threat intelligence, highlight critical attack paths, easing burdens on IT staff. Helps identify gaps in protection and incident impact to support compliance.
Operator-instigated sandbox investigation helps you make informed decisions on suspicious files
Stop the spread of suspicious files or processes detected by EDR to other machines
Instantly terminate suspicious processes to stop potential live breaches
Block connections to and from endpoint to stop lateral movement and further breaches while investigating incidents
Execute remote commands on any workstation for immediate reaction to ongoing incidents
Configurable dashboards and comprehensive instant and scheduled reporting capabilities
Configurable dashboard and email notifications
Supports further integration with 3rd party tools
Low CPU, RAM, diskspace usage
Easy-to-use cloud-delivered management